A taxa na qual os desenvolvedores vazaram segredos críticos de software, como senhas e chaves de API, saltou pela metade, chegando a 5,5 em cada 1.000 confirmações nos repositórios do GitHub.
Isso é de acordo com um relatório publicado pela empresa de gerenciamento de segredos GitGuardian esta semana. Embora a porcentagem pareça pequena, no geral, a empresa detectou pelo menos 10 milhões de casos de vazamento de segredos para um repositório público, representando mais de 3 milhões de segredos únicos no total, afirmou a empresa em seu relatório “2022 State of Secrets Sprawl”.
Embora as senhas genéricas representem a maioria (56%) dos segredos, mais de um terço (38%) envolvia um segredo de alta entropia que inclui chaves de API, sementes geradoras de números aleatórios e outras cadeias de caracteres confidenciais.
À medida que mais empresas movem sua infraestrutura de aplicativos e operações para a nuvem, chaves de API, credenciais e outros segredos de software se tornam essenciais para a segurança de seus negócios. Quando esses segredos vazam, os resultados podem ser devastadores ou, no mínimo, caros.
“Secrets are the crown jewels of any business or organization — they really can grant access into all of your systems and infrastructure,” says Mackenzie Jackson, security and developer advocate at GitGuardian. “The risk can be anything, from complete system takeovers, to small data exposures, or various other things.”
“Millions of such keys accumulate every year, not only in public spaces, such as code-sharing platforms, but especially in closed spaces such as private repositories or corporate IT assets,” GitGuardian stated in its “2023 State of Secrets Sprawl” report.
And even those private spaces can be vulnerable. In January, for instance, collaboration and messaging platform Slack warned users that a “limited number of Slack employee tokens” had been stolen by a threat actor, who then downloaded private code repositories. Last May, cloud application platform provider Heroku, a subsidiary of Salesforce, acknowledged that an attacker had stolen a database of hashed and salted password after gaining access to the OAuth tokens used to integrate with GitHub.
Infrastructure — as … Whoops!
Part of the reason for the increase in leaking secrets is because infrastructure-as-code (IaC) has become much more popular. IaC is the managing and provisioning of infrastructure through code instead of through manual processes, and in 2022, the number of IaC-related files and artifacts pushed to GitHub repositories increased by 28%. The vast majority (83%) of files consisting of configuration files for Docker, Kubernetes, or Terraform, according to GitGuardian.
IaC allows developers to specify the configuration of the infrastructure used by their application, including servers, databases, and software-defined networking. To control all those components, secrets are often necessary, Jackson says.
“The attack surface keeps expanding,” he says. “Infrastructure-as-code has become this new thing and it’s exploded with popularity, and infrastructure needs secrets, so infrastructure-as-code [files] often contains secrets.”
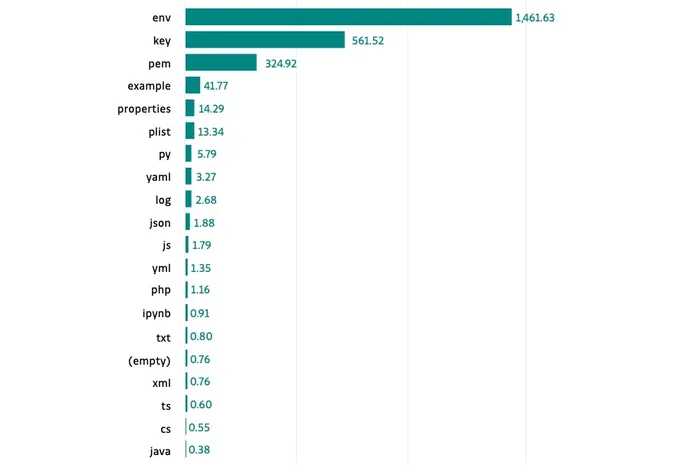
In addition, three filetypes commonly used as caches for sensitive application information — .env, .key, and .pem — are considered the most sensitive, defined as having the most secrets per file. Developers should almost always avoid publishing those files to a public repository, Jackson says.
“If one of these files is in your Git repository, then you know you have holes in your security,” he says. “Even if the file doesn’t contain secrets, they just should never be there. You should have prevention in place to make sure that they’re not there and alerting in place to know when they are there.”
For that reason, companies should continuously scan systems and files for secrets, gaining visibility and ability to block potential dangerous files, Jackson adds.
“You want to scan all of your infrastructure to make sure you have visibility” he says. “And then the next steps include implementing tools to check engineers and developers … to detect any secrets when they slip out.”
FONTE: DARK READING
