Views: 1146
 0
0
 0
0
Read Time:0 Second
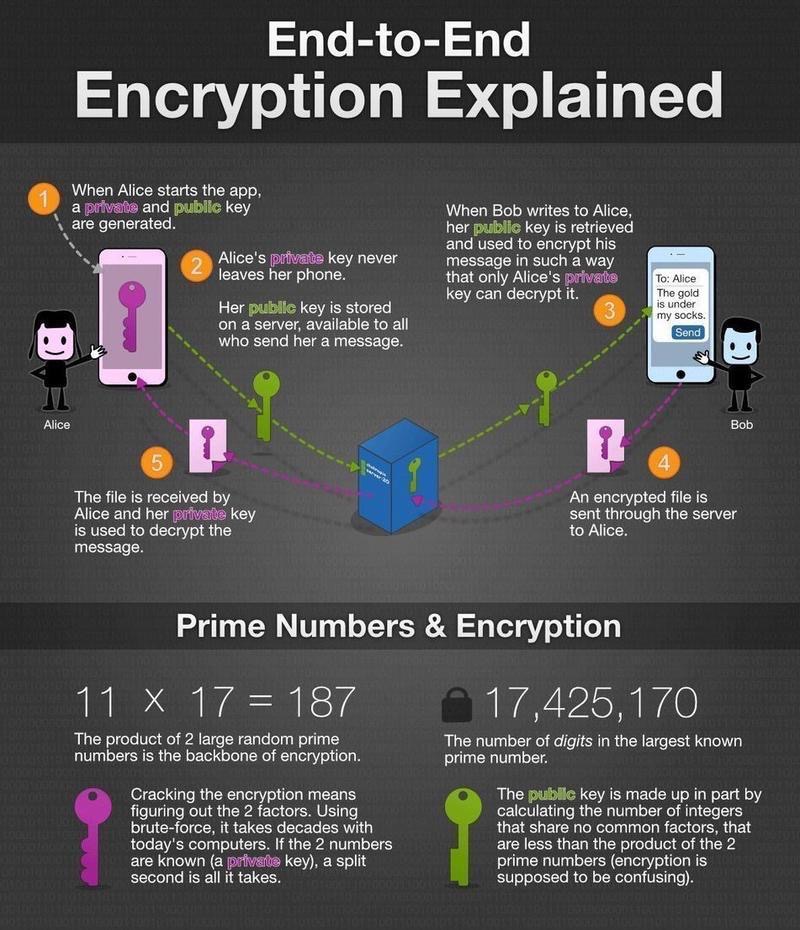
Início » Cibersegurança » End-to-End Encryption Explained
A adoção acelerada de inteligência artificial generativa trouxe ganhos importantes de produtividade, automação e eficiência operacional para empresas de diferentes
A computação quântica deixou de ser um conceito distante para se tornar uma preocupação concreta nas estratégias de cibersegurança corporativa.
*Por José Ricardo Maia Moraes O Harvest Now, Decrypt Later deixou de ser um risco futuro para se tornar um